-
Symantec Messaging Gateway authentication bypass
When conducting security assessments sometimes there is no quick way past external perimeter of the customer’s network. As a last resort option one may commit to an extensive research of the few software appliances the client has exposed. This approach will often yield results, as it was the case with Symantec Messaging Gateway.
-
PlaidCTF 2017 "bigpicture" write-up (pwn 200)
Task description:
Size matters!
We’re presented with a x86_64 ELF binary, libc it’s using and the source code.
$ nc bigpicture.chal.pwning.xxx 420 Let's draw a picture! How big? 1 x 1 > 0 , 0 , A > q A Bye! -
CVE-2017-3881 Cisco Catalyst RCE Proof-Of-Concept
Do you still have telnet enabled on your Catalyst switches? Think twice, here’s a proof-of-concept remote code execution exploit for Catalyst 2960 switch with latest suggested firmware. Check out the exploit code here. What follows is a detailed write-up of the exploit development process for the vulnerability leaked from CIA’s archive on March 7th 2017 and publicly disclosed by Cisco Systems on March 17th 2017. At the time of writing this post there is no patch available. Nonetheless there is a remediation - disable telnet and use SSH instead.
-
A Red Teamer's guide to pivoting
Penetration testers often traverse logical network boundaries in order to gain access to client’s critical infrastracture. Common scenarios include developing the attack into the internal network after successful perimeter breach or gaining access to initialy unroutable network segments after compromising hosts inside the organization. Pivoting is a set of techniques used during red team/pentest engagements which make use of attacker-controlled hosts as logical network hops with the aim of amplifying network visibility. In this post I’ll cover common pivoting techniques and tools available.
-
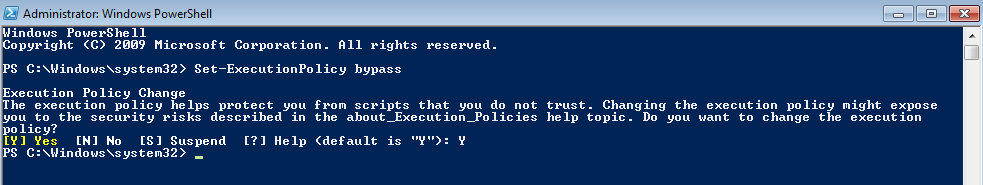
Pentesting Windows environments: remote delivery of PowerShell payloads
PowerShell is an amazing post-exploitation tool available to the attacker during engagements in Windows environments. Tools like PowerSploit or PowerShell Empire help out a lot during internal test. Problem is, restrictive execution policy is enabled by default on windows machines which makes it problematic to run ps1 scripts. Not having admin rights on the target machine means you basically confine yourself to executing PowerShell one-liners which have length restrictions (cmd.exe has a limit of 8191 characters).
One way to bypass execution policy is to gain admin rights on the target and “unrestrict” the execution of PowerShell scripts with Set-ExecutionPolicy cmdlet. It’s a global settings so don’t forget to change in back.